
Precision Engineered for
Cyber Staffing Growth
We don't guess. We execute a rigorous, cyclical process designed to identify, verify, and convert high-value IT & Cyber Security opportunities.

We don't guess. We execute a rigorous, cyclical process designed to identify, verify, and convert high-value IT & Cyber Security opportunities.
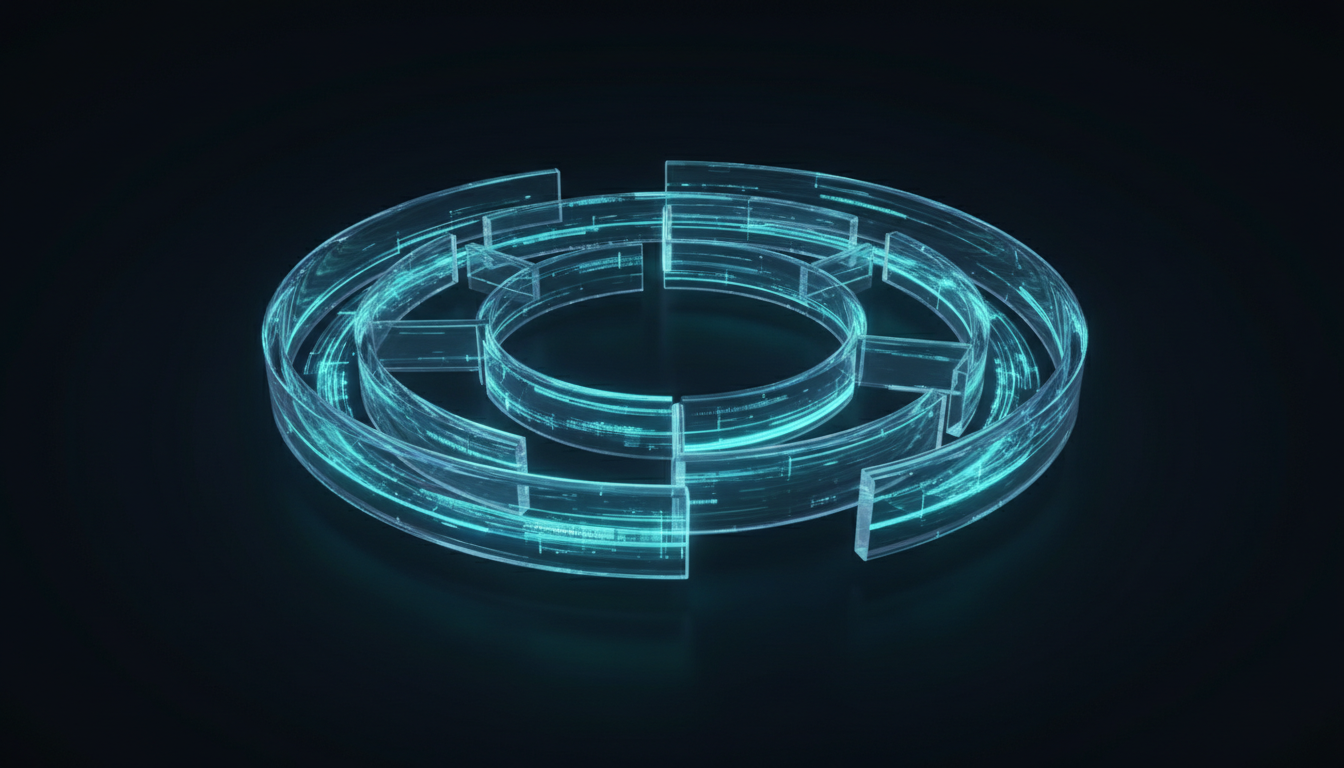
Success isn't a straight line; it's a flywheel. We start with deep analysis, execute with precision, and then use data to optimize and accelerate your results week over week.
Deep dive into your ICP and market positioning.
Multi-channel outreach and triple-check verification.
Weekly pivots based on real-time campaign data.
Scaling what works and eliminating what doesn't.
We don't start until we understand. Every engagement begins with a comprehensive Discovery Call and the creation of a detailed Ideal Customer Profile (ICP). We map your perfect client—from tech stack to company size.
Data is useless if it's wrong. We employ a proprietary Triple-Check Verification Method:
1. AI-driven scraping of job boards and signals.
2. Human verification of contact details.
3. Direct validation to ensure "High Intent."
Generic scripts fail in Cyber Security. Our US-Based SDRs are trained in cyber terminology. We execute a multi-channel cadence (Email + LinkedIn + Cold Call) to book meetings with CTOs and CISOs who actually want to talk.
For staff augmentation, we don't just check resumes. Candidates must pass a rigorous Cyber Security Knowledge Test and have proven past experience. We ensure they speak the language before they ever speak to your candidates.
We don't "set and forget." You receive Weekly Reports and we hold strategy calls to discuss campaign performance. If a tactic isn't working, we make data-backed pivot decisions immediately.
We stand behind our data and our people.
"If a lead is invalid, or an appointment is a no-show, we replace it. Period. We are partners in your growth, and we only succeed when you do."
Let's build your Ideal Customer Profile and start filling your pipeline.
Book Your Discovery Call